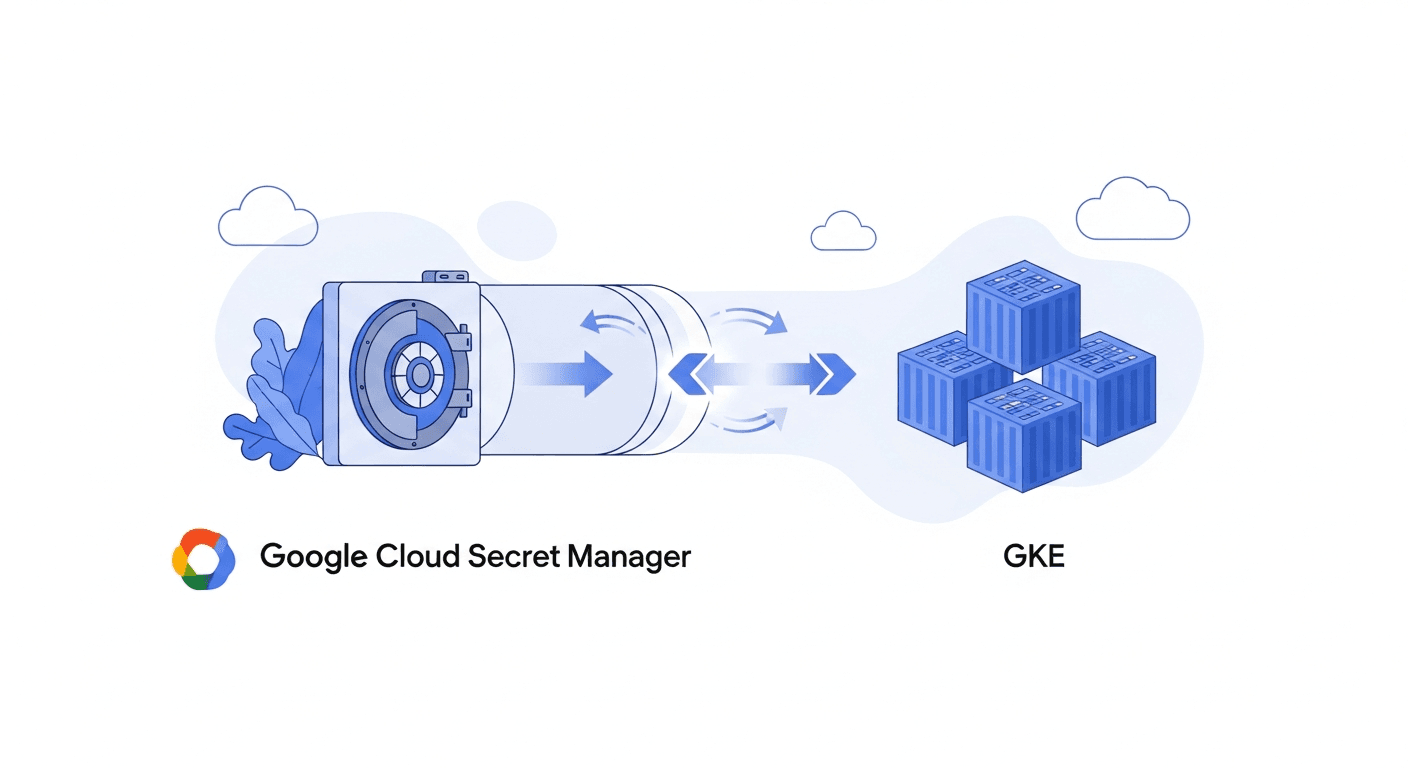
Finally! Sync Google Cloud Secret Manager Secrets to GKE Automatically
11h ago · 2 min read · If you've ever dealt with secrets in Kubernetes, you know it can be a bit of a headache. Keeping sensitive data like API keys, database credentials, or configuration bits secure and up-to-date across your Google Kubernetes Engine (GKE) clusters has t...
Join discussion