I'm a software developer by background. My working day is spent mostly focused on how to create software and only occasionally on how others might break it.
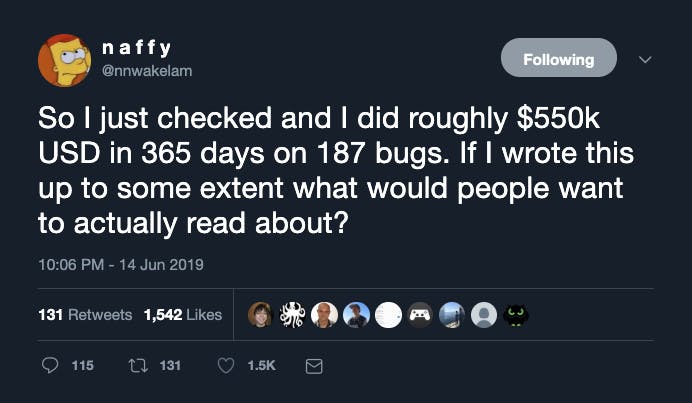
18 years ago, when I started getting into tinkering with software, bug bounties weren't a thing. Although it seems many of the tools people use to win them are the same ones I've been using since then. Recently a colleague left his software security role to look for bugs for a living and then the other day I saw @naffy tweet that he'd made $550k in 365 days on 187 bugs.
That's more than I make building software, for some it would be 10x more.
So when I had a spare couple of hours I decided to look up bug bounty programmes. I picked a popular one that claimed to have a large following and plenty of payouts and looked through it for some participating sites. A large computer manufacturer was listed, it looked a fairly boring target that might not interest many people so I figured it was ideal.
I found an error page where some of the URL parameters were appearing in the body of the page and thought there might be some XSS opportunities there so I fiddled with the parameters for a bit but couldn't get past the escaping. After a while I gave up and moved on, finding a plain HTTP link which seemed an issue in itself but my browser redirected me to use HTTPS and alerted me to a certificate error - the common name on the certificate didn't match the hostname.
At this point I went back to the bug bounty programme page and saw that the deep pockets of the computer manufacturer didn't extend to paying for any bugs, regardless of severity. Still, I'd want to know about this on any site I was running so I decided to submit it anyway. At this point I had to dig into CVSS scoring, which was entirely new to me, but it was relatively straightforward for my first submission. I felt quite pleased with myself at this point, having read about the difficulties some people, admittedly from non-software backgrounds, had in simply getting their feet under the table.
So I moved on, finding a programme that did offer financial rewards, at least for sufficiently high priority issues. After looking past a few websites that were virtually static or ones that you'd have to have a paid account to poke around in I settled on a test version of a shopping site. There were relatively few live product pages off the front page so I looked under the logged in account profile. After clicking through a few pages I hit upon the marketing preferences and something caught my eye.
In the body of the request to update the marketing preferences was the email address of the logged in user. That shouldn't be necessary because the server side code should know the email of the currently authenticated user, but it's perfectly possible to have the client send that information and the server validate it. Still, it was suspicious enough that I decided to create another account and verify it.
Jackpot. I could turn on or off the marketing preferences of another authenticated user simply by changing the email address to that of a different account. Which means if I could get a list of emails off the site (something considered trivial and therefore excluded from a bounty) I could disable the marketing preferences for every user. It seemed a moderately severe issue to me, but in categorising it as an authentication bypass the priority was higher than I might have personally rated the issue. That left me feeling a small rush, perhaps I was beginning to understand why people enjoyed this.
Something in the back of my mind was telling me it wouldn't work out for some reason or another but I couldn't think of anything. Maybe it would be downgraded, but frankly scoring any hit within a couple of hours would leave me feeling pretty content with that as a start. I should have realised that I'd already read about the reason reports are often rejected; sorry, it's a duplicate. A duplicate... of course and a wave of cynicism crept over me until I read a little further and it was replaced with mild frustration. They didn't believe it to be an issue with their system because they were just forwarding the request to a third party who was sending the marketing emails. They even suggested I contact the third party to see if they have a bug bounty programme.
Obviously, I didn't. The third party marketing service didn't authenticate me and can't tell if I'm a legitimate user or not. They authenticate me, they forward the request on, they have to do the validation check.
Gutted.
I was in two minds about replying. I'd read through the material warning not to threaten them, not to release details of any bugs found, etc. that screams bad experiences not handled well. It was probably best to just walk away. Still, I felt I couldn't, so I replied, tried to point out why it was a bug at their end and suggested they reinvestigate it, understanding that there was no benefit to me pursuing a duplicate. Finally I thanked them, I still believe it's a good thing companies participate in these.
They didn't reply again. Hopefully the original reporter received their reward but I have my doubts. I mulled over having another look but the experience left me quite deflated. Thousands of others are probably poring over the same sites and even if you find an issue you've no guarantee the host will understand or care enough to address it. Perhaps I don't have the tenacity required.
It strikes me that it's all very one sided. There's no cost to the sites in leaving issues unaddressed. No transparency over duplicate submissions. And it probably tests the ethics of those who find these bugs more than I'd be comfortable with. I'm old and wise enough not to go and disable all those marketing preferences, but I'm not sure I'd have taken the same approach as a teenager.
I'm not sure I'll try again. Even briefly dipping my toe in the water has encouraged me to revisit the security of the systems I build, that might be where I take inspiration next.
I received a terse reply to the first submission later that day. They didn't understand why I was reporting an issue with no financial reward attached and closed it as won't fix.