Feed
Discussion
Reverse Account Takeover via Email Rebinding Causing Forced Privilege De-Escalation
When we talk about account takeover, we usually imagine a familiar story: an attacker steals credentials, hijacks a session, or abuses password reset flows to log in as someone else. This write-up is about something more subtle — and arguably more da...
z-sec.co4 min read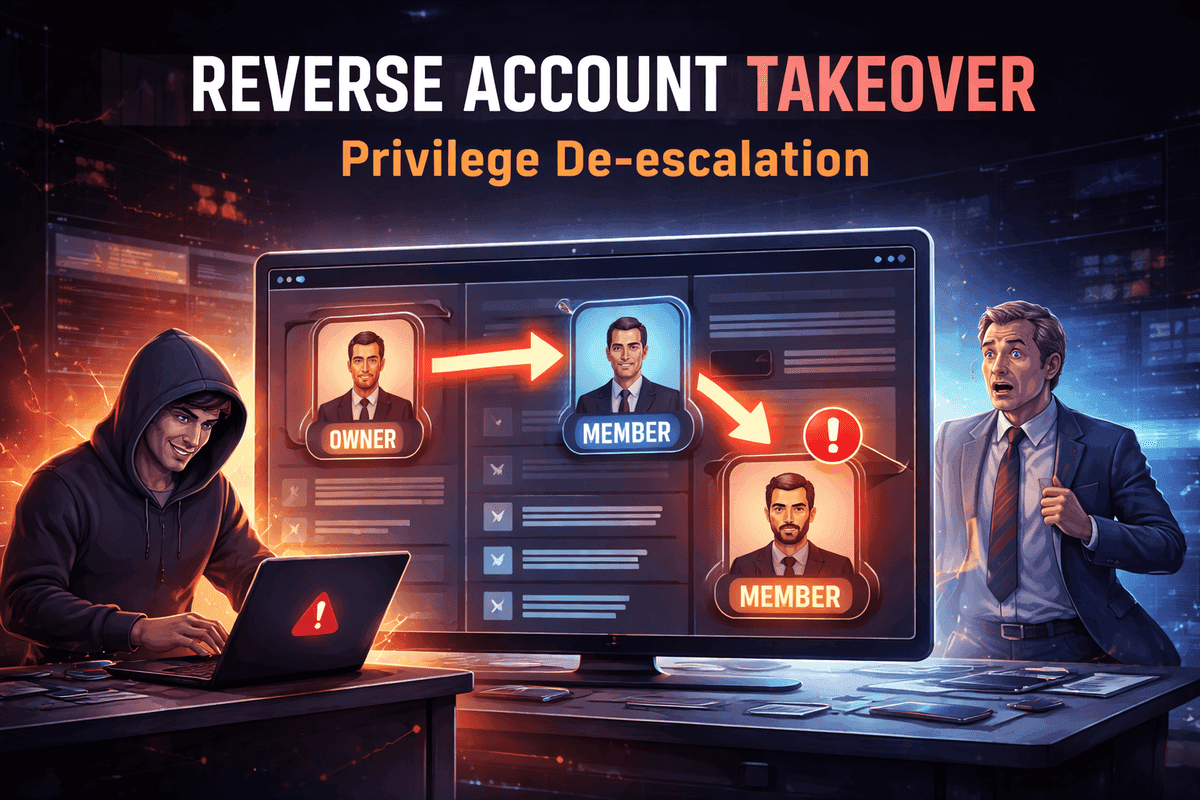
#web-security#account-takeover#privilege-escalation#saas-security#api-security#penetration-testing#ethical-hacking#business-logic
Responses
No responses yet.