May 4 · 6 min read · Part of series: Cloud Security Journey — Zero to Engineer The moment that changed how I see computers happened inside a Windows 10 VM with Task Manager open. I was looking at four processes — smss.ex
Join discussion
May 2 · 5 min read · 📰 Originally published on Securityelites — AI Red Team Education — the canonical, fully-updated version of this article. Technology gets patched. People don’t. Every firewall, intrusion detection system, and endpoint protection platform becomes ir...
Join discussion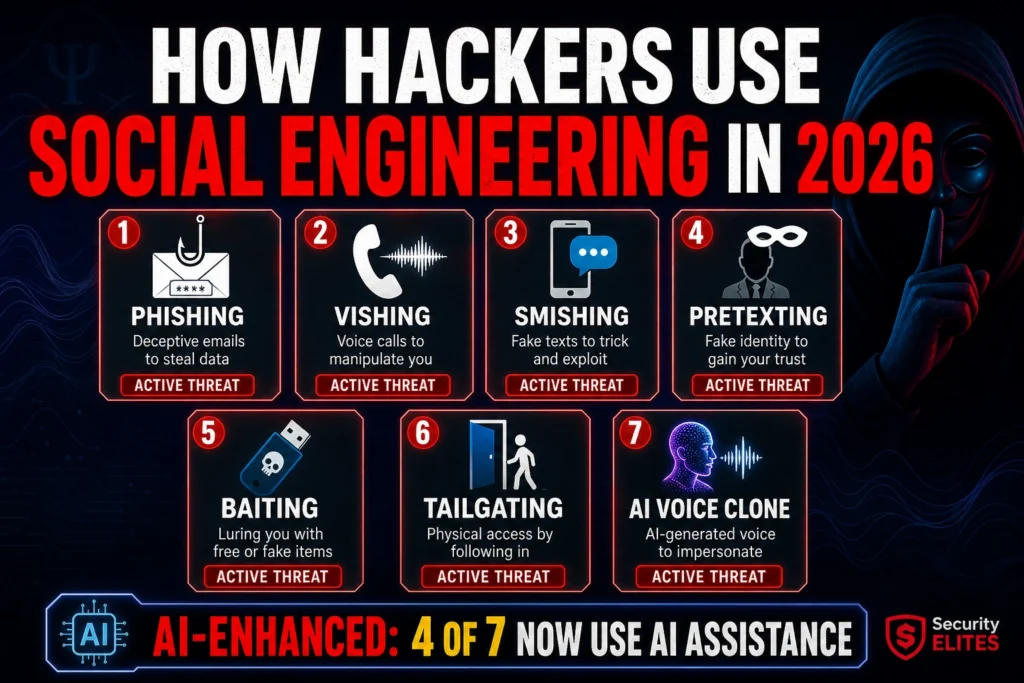
Apr 20 · 7 min read · NeuralStack | MS — Article 1 of 3 Part 1 of the AI Security & Cybersecurity Series The term "penetration testing" gets thrown around liberally in security conversations, often conflated with vulnera
Join discussion