Forums
Thread
Custom Security Review agents for your PRs (browser extension)
Hello peer developers,
I’m sharing a workflow I built over the past few weeks that has made our pull request security reviews more consistent and more actionable.
ThinkReview is a browser extension that works across Git platforms (Gitlab, Github , azure devops and Bitbucket )and runs a custom review checklist based on what your team cares about, such as OWASP guidance and your internal secure coding standards.
Below is a quick look at the end result, then I’ll walk through how I set it up
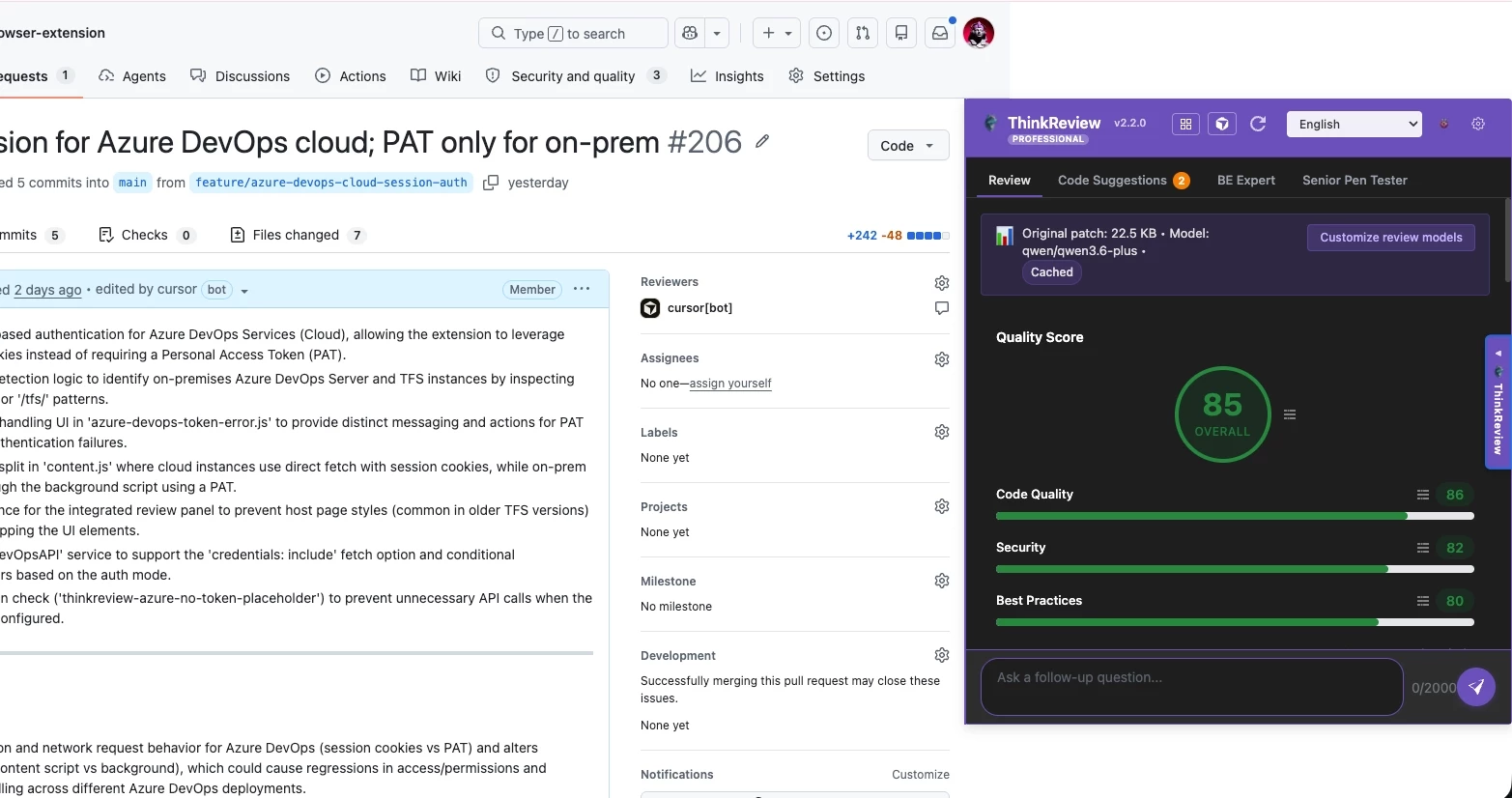
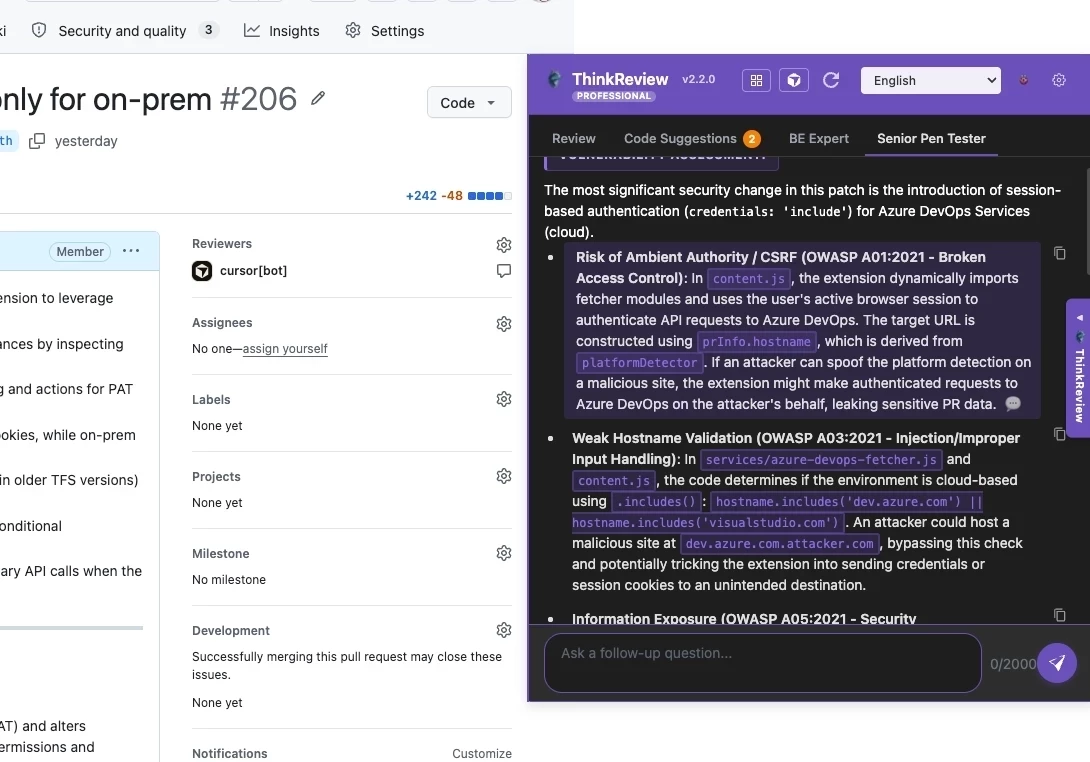
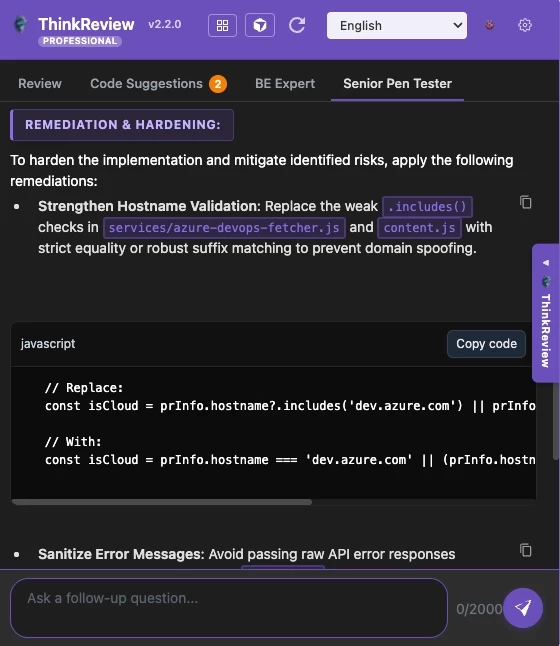
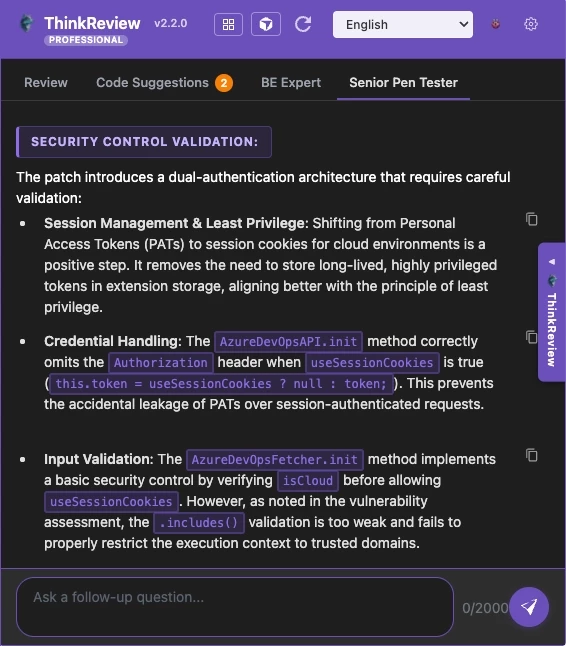
Example: a pentesting-focused review agent
In this example, I created a review agent focused on pentesting.
Define the agent’s goal and scope (what kinds of issues it should look for).
Provide a reference the agent should follow, such as STRIKE Graph best practices. strikegraph.com/blog/pen-testing-best-practices
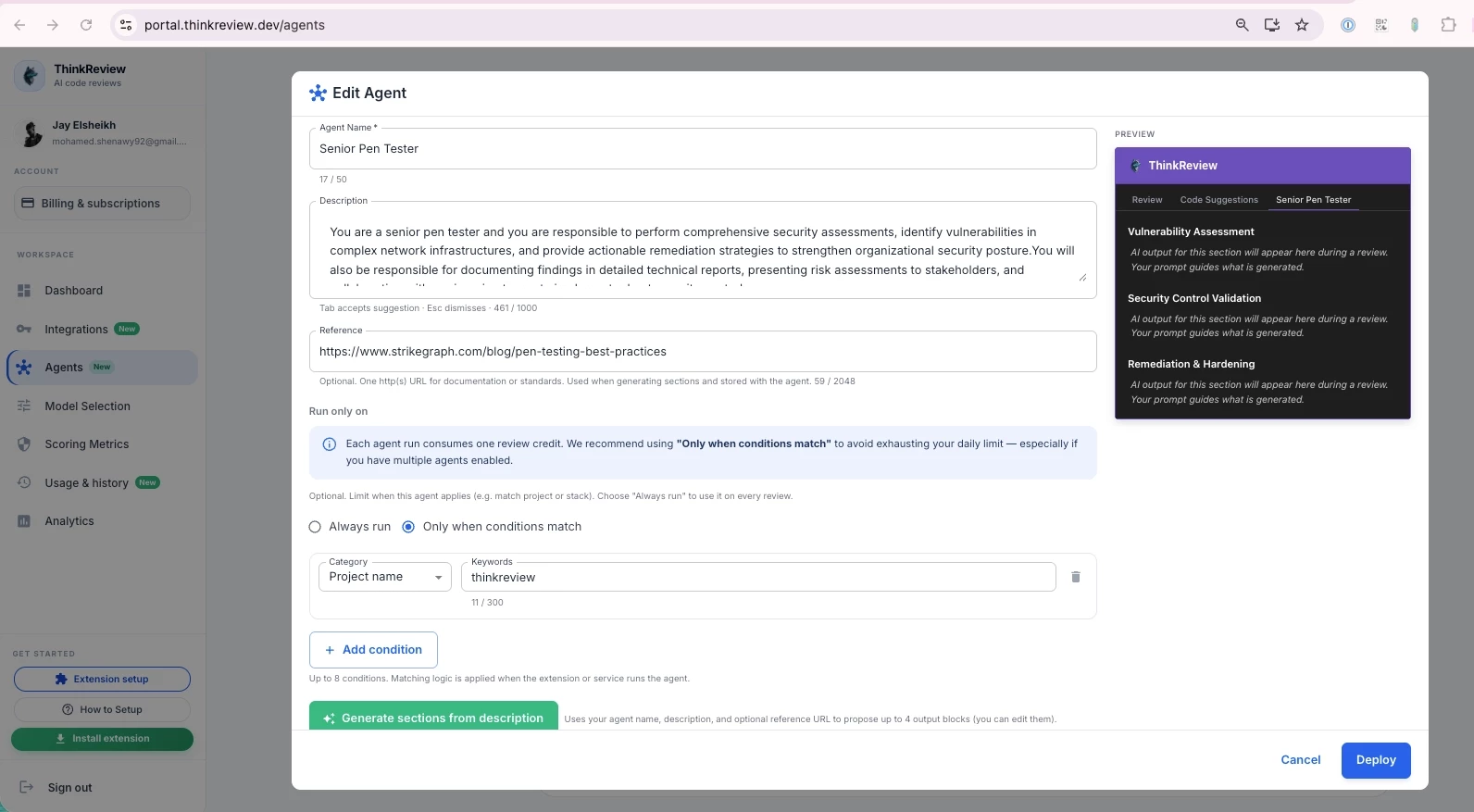
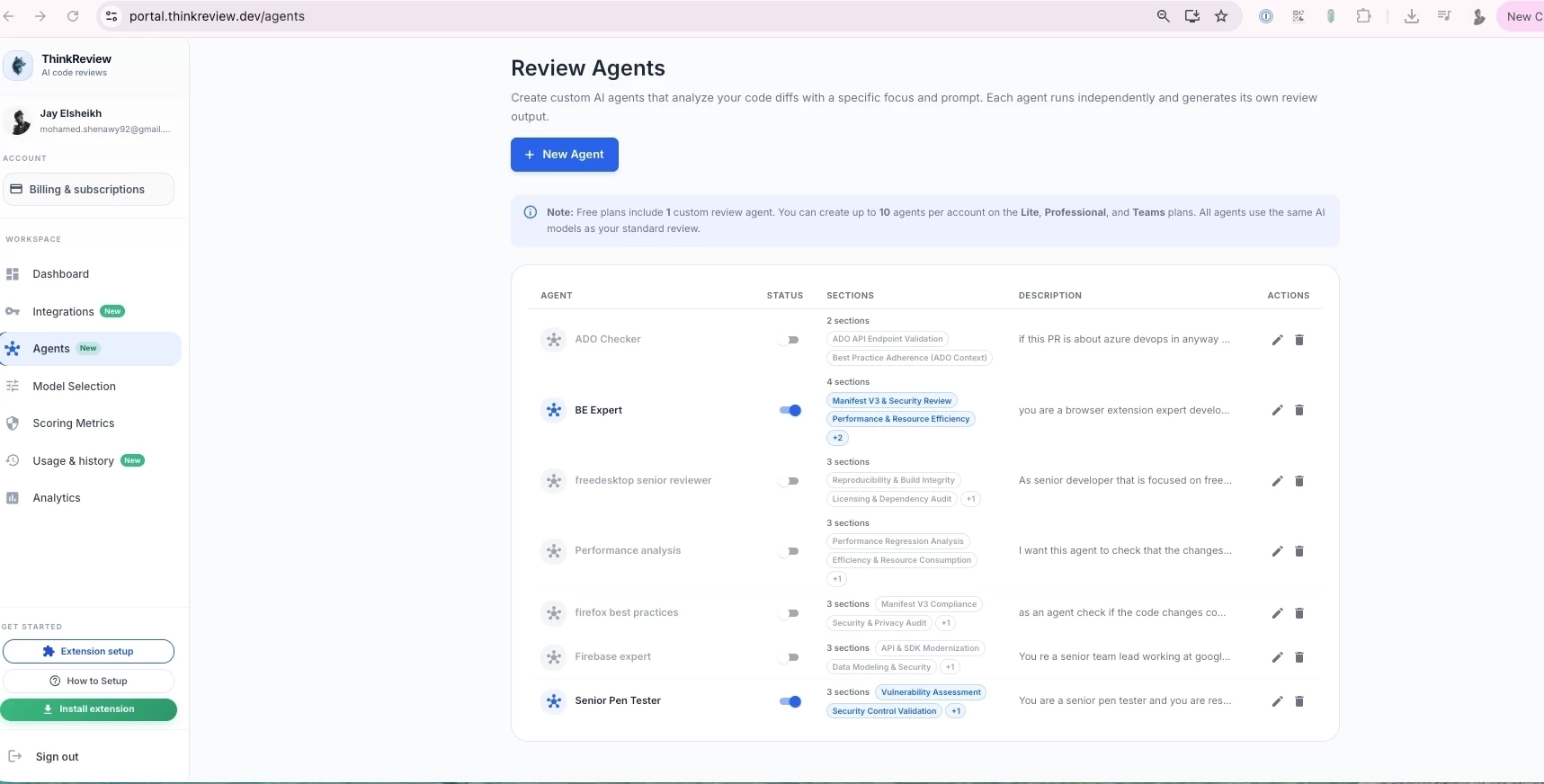
- You can create up to 10 review agent
Run the review on a PR and get findings mapped back to the reference.
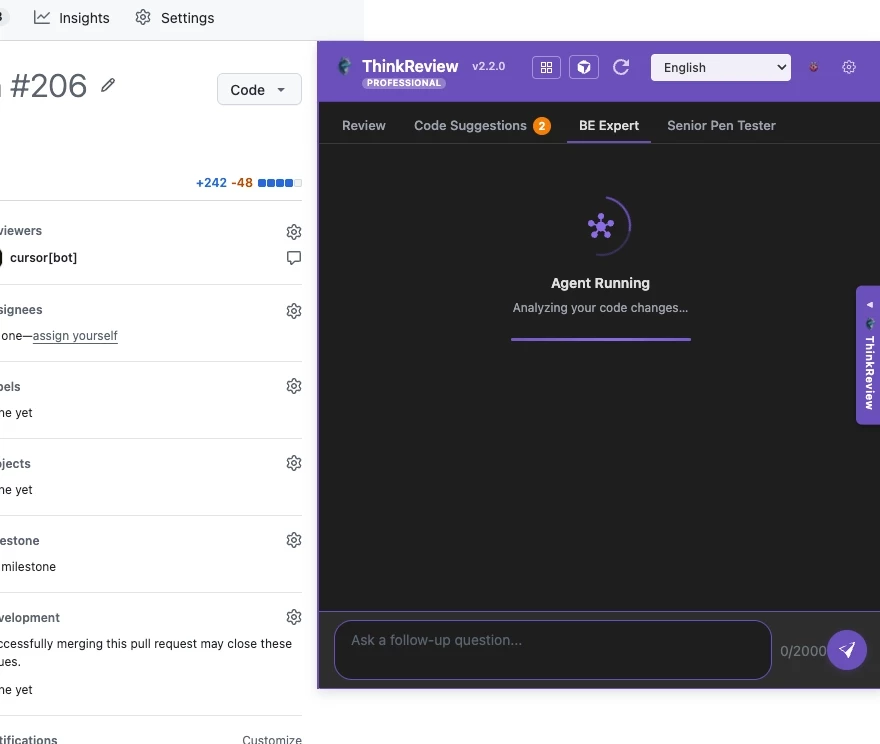
In the PR shown here, ThinkReview flagged a couple of OWASP-related issues using the reference we provided.
The project is open source on Github : github.com/Thinkode/thinkreview-browser-extension
and you can install it from
chrome webstore : chromewebstore.google.com/detail/thinkreview-ai-c…
firefox :
addons.mozilla.org/en-US/firefox/addon/thinkrevie…
**
Read full article here thinkreview.dev/blog/security-agents-workflow-pr-…
Lookin forward to your feedback , any questions would love to hear**
Archit Mittal
I Automate Chaos — AI workflows, n8n, Claude, and open-source automation for businesses. Turning repetitive work into one-click systems.
Running security review as a PR-time agent is a better loop than the usual "run SAST on main, file a Jira, nag the author three weeks later" dance. The signal is fresh, the diff is small, context is in the author's head. One thing I'd test: how well it handles multi-file vulnerabilities (taint from file A → sink in file B via helper in file C). Single-file scanners miss those constantly.