Feed
Discussion
Dec 31, 2023
2. Configuring A Jwt Service For Your Spring Project
In this article, we'd be configuring the various layers of our Security. We'll start with Authentication. This will include a service to generate and validate tokens for a particular user instance , and an Application Configuration class to customize...
timibacco.hashnode.dev4 min read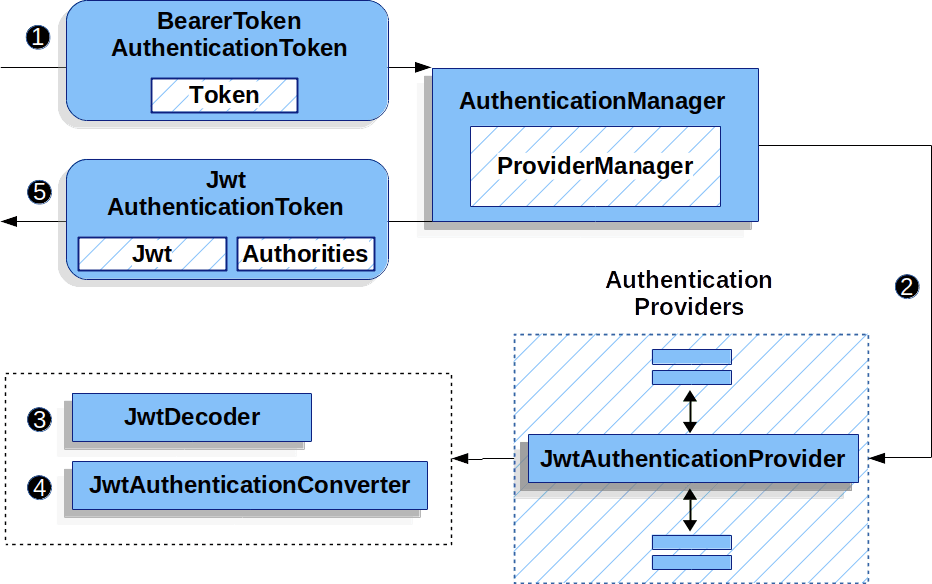
Responses
No responses yet.