Feed
Discussion
Oct 23, 2024
File Upload Vulnerabilities
When files are not uploaded securely, applications are vulnerable. Code injection into the target application by uploading malicious scripts is frequently the first step taken by attackers. The attacker then just has to figure out how to get the code...
beesola.hashnode.dev3 min read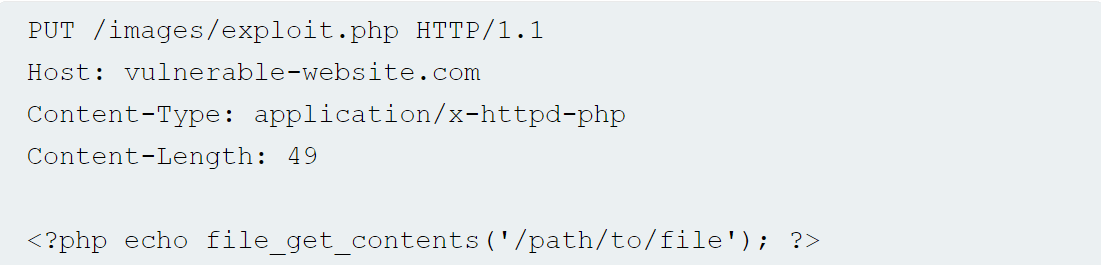
Responses
No responses yet.