Fine-Tuning LLMs: The Complete Engineer's Guide to SFT, LoRA, and RLHF
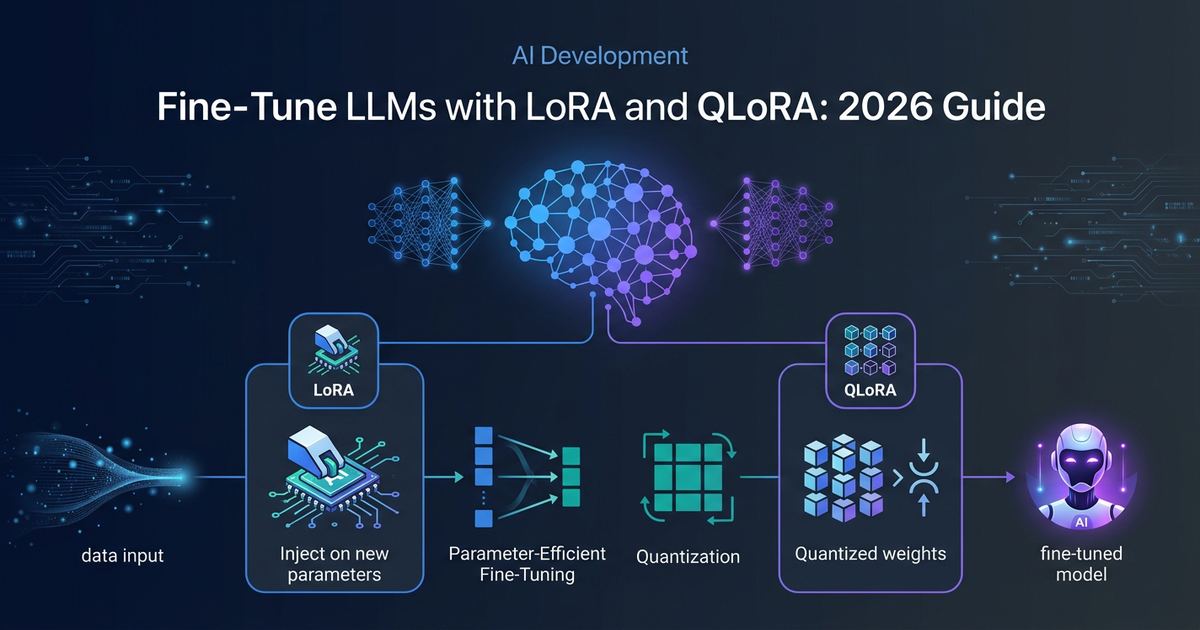
Apr 18 · 30 min read · TLDR: A pretrained LLM is a generalist. Fine-tuning makes it a specialist. Supervised Fine-Tuning (SFT) teaches it your domain's language through labeled examples. LoRA does the same with 99% fewer tr
Join discussion