Feb 22 · 11 min read · Challenge Description Welcome to the Storybook Workshop! In this post, we are going to break down Cider Vault, an incredibly well-designed CTF challenge that serves as a masterclass in modern Linux he
Join discussion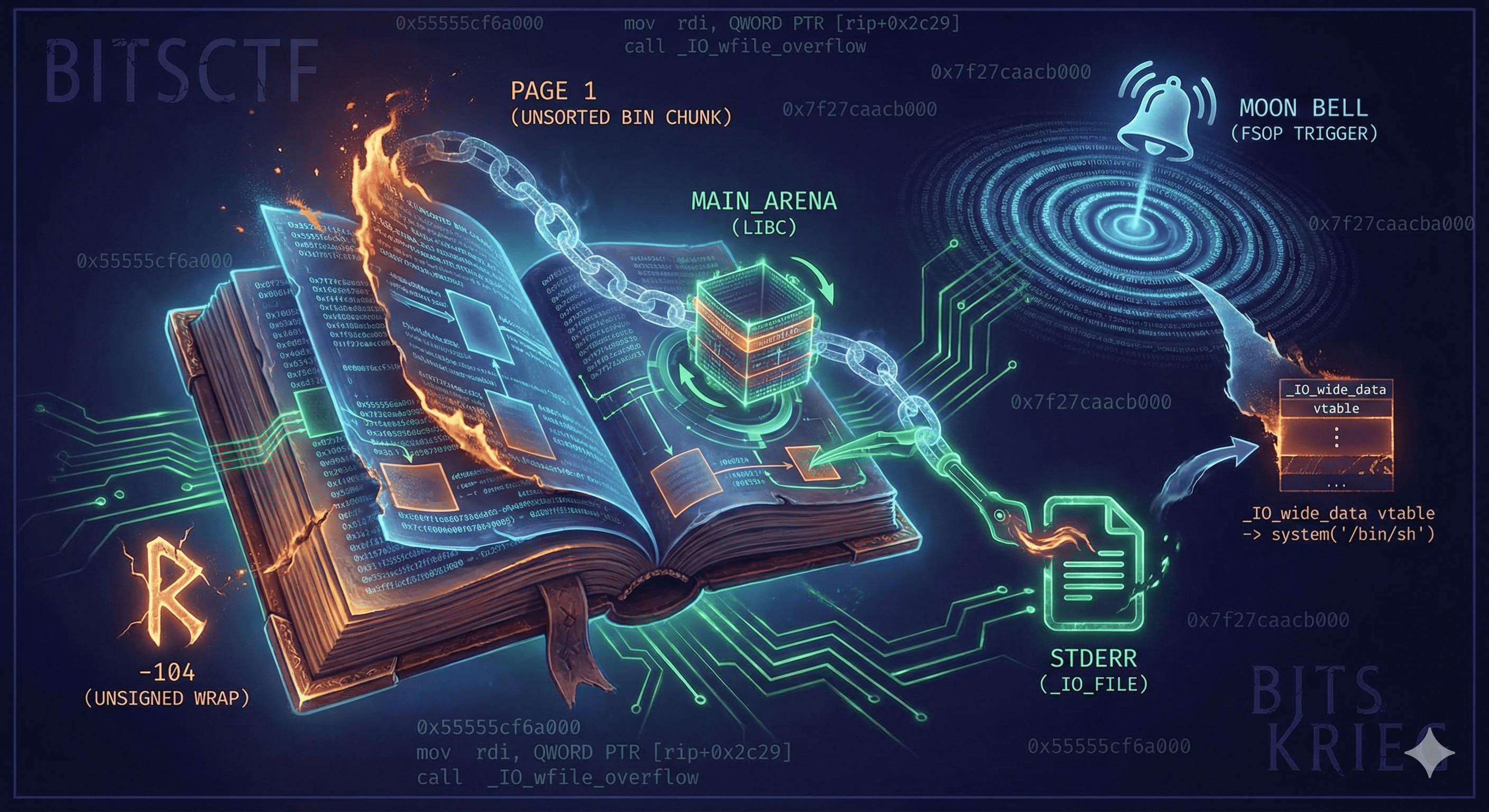
Jan 1 · 9 min read · Challenge Description Category: Binary ExploitationAuthor: _avyra The Krampus Syndicate relies on small, deliberate changes to control systems without replacing them. This binary was used during an intrusion to apply a precise modification to an exis...
Join discussion
Jan 1 · 7 min read · Challenge Description Category: Binary exploitation Author: qvipin The KRAMPUS Syndicate has been using a small remote endpoint they quietly dropped on compromised NPLD machines. When they gain access to a system, they connect to this endpoint and fo...
Join discussion
Dec 13, 2025 · 5 min read · Challenge Description Category: Pwn / Binary Exploitation Author: M0H1.T3L We lost Something, Can you Find it! Solution Walkthrough Initial Reconnaissance and Protection Analysis We begin by analyzing the binary's file type and security protections ...
Join discussion
Jul 20, 2025 · 3 min read · week นี้ไม่ค่อยว่างมีนัดไปนู่นนี่ ว่างเล่นข้อเดียว ถือว่าแปลกใหม่พอสมควร ไม่เคยทำ pwn บน python เลยจั้บ มาดูกันว่าถ้าเรา Arbitrary Write บน Python เราทำไรได้บ้าง โจทย์ให้มาหนึ่งไฟล์ fakeobj.py สั้น ๆ ง่าย ๆ คือ write ได้ 72 bytes ทับที่ตัวแปร obj ที่...
Join discussion
Jun 27, 2025 · 2 min read · Objective: In this level, without the aid of source code, use cyclic patterns and core dump analysis to automatically find the return address and exploit a stack overflow to read the /flag file. Solution: After analyzing the given file pwntools-tutor...
Join discussionJun 27, 2025 · 1 min read · Objective: Here i see some text like chinese , i directly moved to source code for understanding the objective by which i made below table , we have to create/edit notebooks to match this exact pattern. NotebookContentStatus 0"hello "CREATED (...
Join discussionJun 27, 2025 · 1 min read · Objective: This level requires you to write an assembly code snippet to meet the following condition to bypass the check, and use the asm API from pwntools to compile the assembly code and complete the challenge. The condition for this challenge is: ...
Join discussionJun 27, 2025 · 2 min read · Objective: This level requires you to write an assembly code snippet to meet the following condition to bypass the check, and use the asm API from pwntools to compile the assembly code and complete the challenge. The condition for this challenge is: ...
Join discussion