GPU Tracing With cgroup Awareness: Per-Tenant Investigation on Shared Hosts
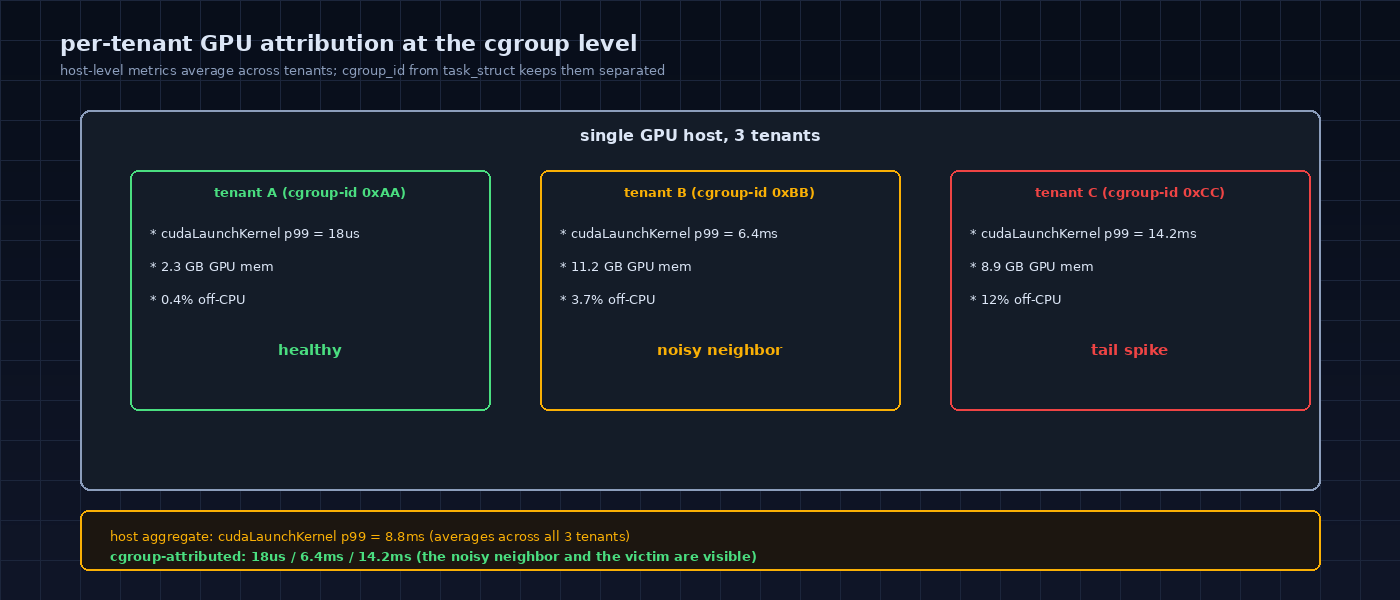
1d ago · 4 min read · On a shared GPU host, the kernel knows which container generated which event. The trace stays separable as long as cgroup_id rides along. TL;DR On a shared GPU host (think K8s with three GPU pods, or
Join discussion